- What is needed for an architecture practice?
Three people have shaped my thinking on IT Architecture Governance more than anyone else: Andrew Townley, Neil Rerup, and John Czaplewski.
The link below is from Neil — and if you’re trying to build or mature an Architecture Practice, it’s one of the best blueprints I’ve come across.
www.linkedin.com/pulse/ecsas-reference-architecture-practice-neil-rerup-yoiyc
- What does Lego have to do with Cybersecurity Architecture?
Great question! Despite the risk of spoiling future “ice breakers,” let me share an exercise that answers the question through action. Enough talking—no academic architects needed today!
- Purchase 3-4 identical LEGO kits, each containing between 100-200 pieces. Choose a set that aligns with your organization’s field. For instance, if you’re in healthcare or manufacturing, opt for a car model.
- Unbox all the kits, combine all the pieces into a single bag, mix them thoroughly, and then pour them into a pile.

3) Show a “rules” slide. Below is an example from the last exercise.
4) organize the participants into group of 2-3 people
5) tell people to start.
So, what typically happens next? Well, people love building with LEGO bricks—who doesn’t, right? In every instance I’ve run this exercise, everyone immediately starts grabbing pieces and building something. Why do they do this? Maybe they’re eager to relive fond childhood memories. Perhaps they’re doers who just want to complete the task. Or maybe they feel the competitive pressure of the timer. Regardless, the architects communicate with each other and have a great time. While no one has burst into singing “Everything is Awesome” (see this https://youtu.be/9cQgQIMlwWw?si=ODUGkwCohYu8eeuK), I usually walk around, taking pictures to capture their progress and final creations.




Now, you might be curious about how I handle questions. For this exercise, I used Microsoft Copilot to create a fictional press release between onsemi and Waymo. Depending on the question, I would share this press release.. I have highlighted some key “attributes” within the press release. If you noticed the quotes around “attributes,” you’re right—they refer to SABSA business attributes.
Fictional Press release by Microsoft Co-pilot–
Press Release
onsemi and Waymo Announce Strategic Partnership to Develop Solar-Powered Autonomous Vehicles with Open Design Access
Phoenix, AZ – September 21, 2024 – onsemi (Nasdaq: ON), a leader in intelligent power and sensing technologies, today announced a strategic partnership with Waymo, an autonomous driving technology company, to develop a new generation of solar-powered autonomous, 1 person automobile. This collaboration aims to integrate onsemi’s advanced semiconductor solutions with Waymo’s state-of-the-art autonomous driving systems to create a sustainable and efficient transportation solution. Additionally, the partnership will make the vehicle design available to the public, encouraging innovation and collaboration within the industry.
Hassane El-Khoury, CEO of onsemi, stated:
“We are thrilled to partner with Waymo on this groundbreaking project. This partnership not only represents a significant advancement in sustainable and autonomous transportation but also embodies our commitment to open innovation. By making the design of our solar-powered vehicle available to the public, we aim to foster a collaborative environment where innovators and enthusiasts can contribute to the future of mobility.”
Key Requirements of the Partnership:
- Integration of Solar Technology: The vehicles will be equipped with advanced solar panels to harness renewable energy, significantly reducing the reliance on traditional fuel sources.
- Advanced Semiconductor Solutions: onsemi will provide high-efficiency power management and sensing technologies to optimize the vehicle’s performance and energy consumption.
- Autonomous Driving Systems: Waymo will integrate its latest autonomous driving technology to ensure safe and reliable operation of the vehicles.
- Sustainability Goals: Both companies are committed to achieving significant reductions in carbon emissions and promoting the use of renewable energy in the automotive sector.
- Open Design Access: The partnership will release the vehicle design to the public, allowing engineers, developers, and hobbyists to access and contribute to the development of solar-powered autonomous vehicles.
Innovation and Development: The partnership will focus on continuous innovation and development to push the boundaries of what is possible in autonomous and sustainable transportation.
About onsemi: onsemi (Nasdaq: ON) is driving disruptive innovations to help build a better future. With a focus on automotive and industrial end-markets, the company is accelerating change in megatrends such as vehicle electrification and safety, sustainable energy grids, industrial automation, and 5G and cloud infrastructure. onsemi is headquartered in Phoenix, Arizona, and has a global network of manufacturing facilities, sales offices, and design centers.
About Waymo: Waymo is an autonomous driving technology company with a mission to make it safe and easy for people and things to move around. Since its inception as the Google Self-Driving Car Project in 2009, Waymo has been focused on building the world’s most experienced driver and making it available to everyone.
————————————————————————————————
In this particular exercise, I would have provided the instructions that come with the LEGO set if participants had asked to see the published “open design.”
After the time has elapsed, I ask the following question:
- What does LEGO have to do with cybersecurity architecture?
Here are some answers:
- Efficient, reusable building blocks
- Modularity of the blocks
- Scalability of the blocks.
- Interconnected nature of blocks allow adaptable and efficient models
All of these answers are accurate. However, the key answer is requirements gathering. How do you know what your customer wants, in this case, the CEO of onsemi, if you don’t ask them? If participants had asked “great questions,” as Andrew Townley always advocates, I would have given them pieces of paper with attributes important to Hassane in this fictional scenario.

Of course, you can potentially guess some of the things the customer wants. For example, in this instance, each team created a solar-powered car and a one-person car. You can see the check marks beside the attributes in the picture. However, the teams missed the business objectives of the Waymo partnership: safety and autonomy. How does the final product compare to the imaginary one that Hassan had in mind?

What does this mean? We should always help our customers deliver value. We cannot be roadblocks, even ones made of LEGO bricks. We must always prioritize safety. One way to keep them safe is by ensuring we ask and understand their requirements. This increases the likelihood that the operationalized solution meets the needs of the organization. Don’t get too caught up in the pressure of a “timer.” Don’t get me wrong. We got to deliver and timelines need to be met. Pause, do your homework, ask great questions, and get those requirements documented.
- Business Contextual Architecture – Keelson Management, a wholly owned subsidiary of CMA CMG

Figure 1 – Business Contextual Architecture for Keelson Management This is a follow up post to another one that focuses on Port and Terminal Cybersecurity in general. This post focuses on the business contextual architecture of a company responsible for maritime terminal cybersecurity, Keelson Management. This is another use case for The Agile Security System by @Andrew Townley.
Please refer to others postings on The Agile Security System: 1) Overview of The Agile Security System; 2) Overall approach for producing the output for business contextual architectures and initial observations; 3) the efficiency gains via re-use, iterations, and time boxing of this approach; 4) value of this approach – why and help prioritize tactics; and 5) Developing a cybersecurity objectives or business attributes for a cybersecurity strategy based on mitigations to risks to business objectives.
Let me know what you think!
~R&R,
Everyone Needs Some!Initial Observations
- In the realm of Maritime Transport Systems (MTS), it’s imperative for organizations to designate a Cybersecurity Officer (CySO). The CySO’s key responsibility revolves around developing, revising, and disseminating a “Cyber Annex” to Facility Security Officers. This annex serves as a guarantee that the cybersecurity measures and risk mitigation efforts pertaining to the facility’s physical security and safety are pertinent and adequate. Essentially, it serves as a strategic roadmap to tackle the cybersecurity challenges inherent in MTS. You can find more details about the Cyber Annex at this link: Cyber Annex Guide. It’s worth noting that while the Cyber Annex is a robust strategy, it may not encompass all potential cybersecurity vulnerabilities or remedies. Some might wonder about the necessity of introducing the “CySO” role (vs “CISO” by the US Coast Guard). Nevertheless, for MTS organizations like Keelson, ensuring a cybersecurity strategy aligns with the security objectives of being “Assured” and “Compliant” are paramount.
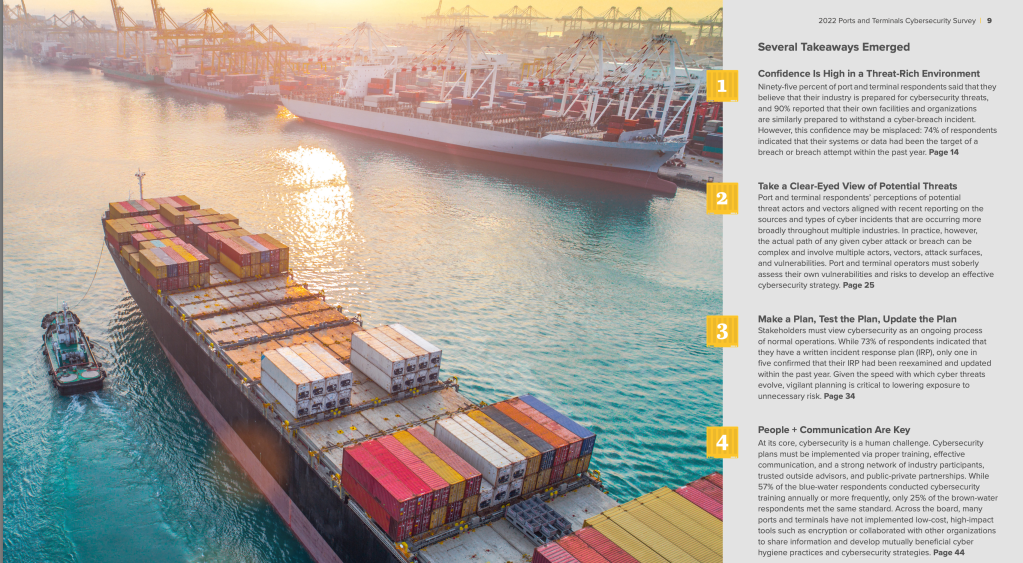
- Like organizations in other industries, effective management of cyber risk is critical to the success of an MTS organization. A successful cyber-attack can lead to several risks for US ports and terminals. Refer to the CISA diagram, the Port Facility Cybersecurity risk, for a list of cybersecurity risk. “Risk-Managed’ and “Integrity-Assured” are critical security objectives of any cybersecurity strategy.
- Maritime ports are a rich environment for cyber-attacks. For example, a recent study from Rutgers shows various scenarios of physical and cyber-attacks against MTS organization. MTS organizations need to recognize that cyber-attacks translate to real business risk and need to manage it. MTS organizations need to understand that threat actors are “burrowing” into their environments in preparation for future conflicts (refer to minute 30 [ish] of the US House Select Committee on the CCP, “The CCP Cyber Threat to the American Homeland and National Security,” dated 01/31/2024) “Risk-Managed,” and “Educated” (about cyber-attacks on their operating environment) are key objectives.
- The MTS is an industry that has a very visible intersection between the physical and cybersecurity worlds. The compromise of operational technology (OT) ships or systems ashore can result in considerable harm to personal safety and security of ships, ports and marine facilities. Facility Security Assessments (i.e., physical security risk assessments) , as required by the US Coast Guard as part of their Navigation and Vessel Inspection Circular No. 01-20 (NVIC 01-20), includes a review of computing systems and networks; the goal is to understand if cybersecurity vulnerabilities can be exploited to compromise physical controls. As such, US Coast Guard provides recommendations that MTS organizations create a traceability matrix between cybersecurity vulnerabilities and their associated physical security vulnerabilities. US Coast Guard also recommends a traceability matrix between cybersecurity protections and the cybersecurity vulnerabilities they remediate. “Safe” and “Compliant” are important security objectives that need to be part of cybersecurity strategy.
- Practice. Practice. Practice. Incident Response, Business Continuity plans and alert triage playbooks all need to practiced on a regular basis. IR plans must include contacting the FBI, US Coast Guard (i.e., Captain of the Port), and CISA. “Usable,” “Documented”, “Maintained” and “Governed” are critical objectives for any cybersecurity program.
- MTS organizations should use the NIST Cybersecurity Framework to measure effectiveness via a maturity assessment and benchmarking with peers. I recommend hiring a 3rd party to complete an initial maturity assessment and require them to provide a benchmark of the MTS sector. It is critical that any target maturity needs to be calibrated with the risk management and governance of the organization (i.e., NIST CsF Profile). The US Coast Guard recommends using the NIST Cybersecurity Framework (CSF) as the preferred framework for aligning cybersecurity protections, which includes a baseline with various maturity levels. To simplify implementation, I suggest mapping the NIST CSF to CIS Critical Security Controls, incorporating the CIS Controls ICS Implementation Guide for more practical guidance on control implementation. It’s crucial to extend this mapping to the MITRE ATT&CK framework and ensure that assessments encompass the scope of technology deployment, procedures, and staffing levels/skills. Technology is at best ineffective at worst useless without process, correct staffing levels and skill sets. I also recommend reviewing NIST’s website for latest information on NIST CsF 2.0, including the new “Govern” function and Informative References. Today, there is no Community Profile specific to MTS, although there is one for the PNT. MTS organizations heavily use PNT. As such, “Compliant” “Usable” “Governed” and “Effective” are key attributes or security objectives.
- Threat intelligence and collaboration is critical between organizations and entities in the MTS; this also applies between CMA CMG corporation and their subsidiaries. MTS organization should participate in and contribute to the Maritime Transportation System Information Sharing and Analysis Center and the annual Maritime Cybersecurity Summit . The MTS-ISAC publishes an annual report outlining trends that MTS should be aware of. For example, the 2023 report provides the following reasons for increased risk for MTS organizations: a) geopolitical tension; b) inability for MTS organizations (or governments) to counter or pushing nation states or criminals for cyber-attacks. c) economy is driving underemployed or unemployed to cybercrime; d) MTS organizations lag behind in technology and require modernization; and e) an increase in 3rd party integrations. CMA appears to have a threat intelligence capabilities based on their advisories regarding conflicts in world. “Threat-Managed” is an important security objective of Keelson Management cybersecurity strategy.
- Due to the heavy use of OT, OT Cybersecurity needs to be prioritized in terms skill set and process. Need specialization and support for Operational Technology. NIST has published a guide on OT Security (NIST SP 800-32r, According to attacks on OT systems in the maritime industry has increased by 900% since 2017 (in 2021; see https://sustainableworldports.org/wp-content/uploads/IAPH-Cybersecurity-Guidelines-version-1_0.pdf).
- It is imperative for MTS organizations to ensure the defensibility of their cybersecurity programs. I recently engaged in a conversation with a former Chief Information Security Officer (CISO) from a chip manufacturing company. Despite having a budget that surpassed many other organizations, he acknowledged that his organization still faced successful cybersecurity incidents. Every MTS organization must acknowledge the inevitability of compromises. These organizations cannot solely rely on outspending or outskilling threat actors, particularly those backed by nation states. For instance, according to Chris Way, the Director of the FBI, the People’s Republic of China (PRC) boasts the largest hacking program globally, surpassing the combined efforts of all major countries and outnumbering U.S. government hackers 50 to 1 (refer to minute 20 of the Select Committee on the CCP, “The CCP Cyber Threat to the American Homeland and National Security,” dated 01/31/2024). Furthermore, a 2023 MTS-ISAC report highlighted a concerning trend where countries tend to police MTS victims of cyber-attacks and attribute blame to them, rather than holding accountable the threat actor groups responsible. A critical cybersecurity objective of any cybersecurity program is “Auditable.”
- Network segmentation is critical for MTS organizations. The US Coast Guard published a simple network architecture that highlights an approach to this segmentation.
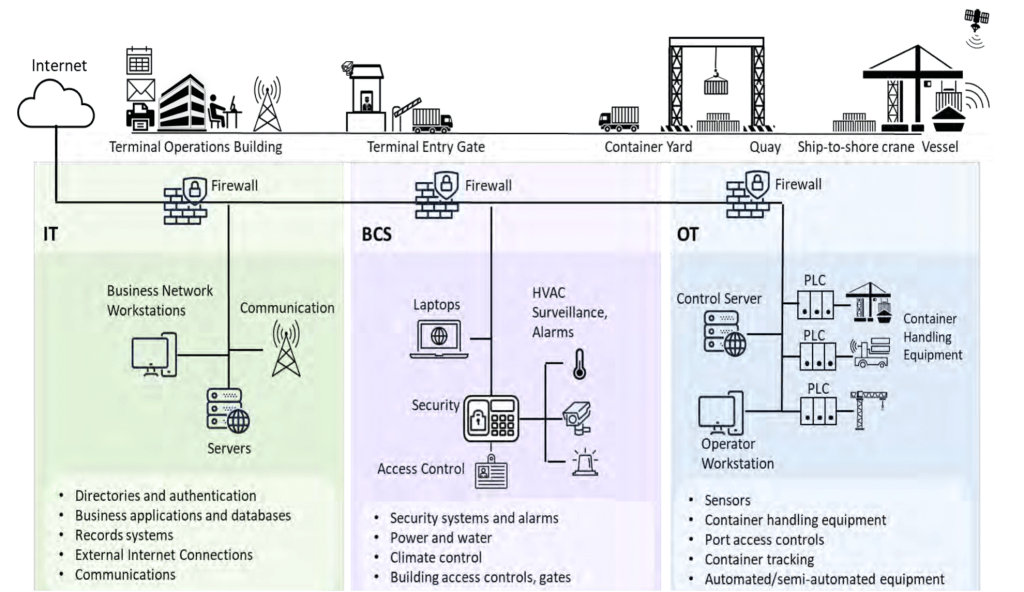
Figure 2 – Basic Architecture for Segmentation Based on System Category Initial Questions
- Is the business contextual architecture correct? What is missing?
- Where do requirements for Keelson come from? Below is a listing of sources for potential requirements for a company, like Keelson, operating seaport container terminals in the US. It is imperative for a company to assign a role to consistently review these sources along with others to draft company specific policies and standards and training material. Cybersecurity staff would have to collaborate with legal and compliance teams. Here is a quick list of potential sources: a) International Association of Ports and Harbors (IAPH); b) US Coast Guard (USCG). US Coast Guard has published several guidance documents: i) Navigation and Vessel Inspection Circular (NVIC 01-20) ; ii) Maritime Cybersecurity Assessment and Annex Guide (MCAAG); c) Cybersecurity and Infrastructure Security Agency (CISA); d) Baltic and International Maritime Council (BIMCO); e) International Maritime Organization (IMO).; f) Jones Walker Survey ; g) ISO/IEC 27001; h) Executive Order on Amending Regulations Relating to the Safeguarding of Vessels, Harbors, Ports, and Waterfront Facilities of the United States; h) NIST Cybersecurity Framework (version 2.0); i) Corporate CMA CMG Policies and Standards.
- Are the roles and responsibilities been clearly defined by CMA and Keelson? Why was Keelson originally setup as a wholly owned subsidiary of CMA?
- Port and Terminal Cybersecurity
Following President Biden’s recent executive order on “Amending Regulations Relating to the Safeguarding of Vessels, Harbors, Ports, and Waterfront Facilities of the United States” I quickly delved into some research and discovered four valuable resources. Side note, one thing that I love about the cybersecurity field is the opportunity to use your expertise to contribute and make a positive impact across various industries.
Port Facility Cybersecurity Risks Infographic

Jones Walker 2022 Ports and Terminals Cybersecurity Survey
International Association of Ports and Harbors (IAPH)

US Coast Guard – Domestic Ports Division

- Business Contextual Architecture – SC Johnson & Son, A Manufacturer and the Value of Re-Usable Architecture
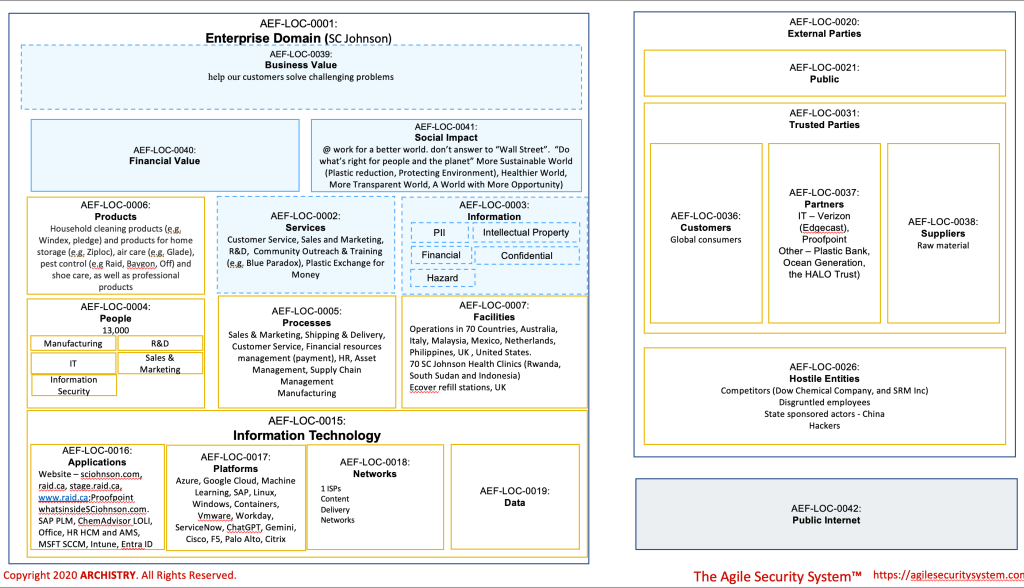
Figure 1 – Business Contextual Architecture (i.e., Domain Impact Worksheet) – SC Johnson Greetings, fellow architect or cybersecurity strategist! Imagine if you had a looming deadline and a meeting scheduled with a stakeholder in just two hours, especially as a newcomer to the company or potentially a new customer, preparation is key.
In tackling this challenge, consider leveraging the Agile Security System (TASS) for a streamlined approach.
Note: for a deeper understanding of the methodology, refer to the insights provided in the Rogers post.
This article, however, won’t introduce new techniques; instead, it underscores the efficacy of TASS, particularly in swiftly delivering a business contextual architecture. The swiftness of TASS is attributed to key factors: simplicity over complicated models in software, a focus on iterations over perfectionism, and a commitment to re-usability.
In terms of re-usability (#3), it’s noteworthy that the domain impact worksheet incorporates elements from another manufacturing company, ON. This re-usability extends beyond the worksheet itself to encompass requirements, risks, mitigations, and even initial observations and questions specific to a particular domain. The versatility of TASS lies in its ability to adapt and apply proven elements across various aspects, facilitating a more efficient and effective approach to cybersecurity strategy. A word of caution though: do not the let beauty of this approach turn you into a “lazy” (not in smart way) and “autopilot architect.”
I prefer to “practice what I preach,” hence I’ve established a two-hour time limit to complete this post. This includes conducting research, developing the domain impact worksheet, formulating observations and questions, and finally, posting the content on the blog. And yes, I leverage ChatGPT to help improve how some of the content is written. Hopefully, ChatGPT doesn’t completely eliminate my personality from the writing!
Let me know what you think!
~R&R,
Everyone Needs Some!Initial Observations
Observation Re-useable Detailed Information SC Johnson must protect their intellectual property (IP Yes See ON Semiconductor posting SC Johnson must have advanced capabilities in intrusion detection, web security, threat intelligence, and training Yes See ON Semiconductor posting SC Johnson security, encompassing both facility and infrastructure, including cybersecurity, is crucial for ensuring safety, operational effectiveness and profitability. Yes See ON Semiconductor posting SC Johnson must gather and keep up with laws and regulations and translating them into physical, administrative, and technical controls Yes See ON Semiconductor posting Note – one unique source of requirements is the US Environmental Protection Agenda List of Lists – Consolidated List of Chemicals SC Johnson must establish an Enterprise Architecture (EA) capability Yes See ON Semiconductor posting
Note – EA function is even more important in light of SC Johnson strategy to make the world a better place through various initiatives (like Base of the Pyramid Team, Blue Paradox)SC Johnson cybersecurity capabilities must encompass attack surface management and threat intelligence Yes See ON Semiconductor posting SC Johnson must have a strategy for cloud governance, process, people and technology. Yes See Rogers Posting Table 1 – Re-usable Observations Initial Questions
Re-useable questions for another manufacturer organization
- Is the accuracy of the business architecture confirmed, and is there any essential component missing?
- Does a reference architecture exist for a specific plant that includes cybersecurity requirements? How is the integration handled in the event of a merger with a new company?
- What role does IT and Cybersecurity play in the expansion or installation of a new manufacturing facility?
- In what ways can Cybersecurity support and safeguard Research and Development (R&D) efforts?
- Is there a defined policy or stance regarding Generative AI, and does SC Johnson have an Emerging Technology Committee in place?
Unique Questions
- What critical applications are needed for the key processes identified?
- How integrated are SC Johnson’s partners in terms of their networks or data sharing?
- Has the executive leadership team written a “risk factors” report (like the risk factor section of a SEC filing)?
-
Subscribe
Subscribed
Already have a WordPress.com account? Log in now.